DenyHosts is a Python script that analyzes the sshd server log messages to determine what hosts are attempting to hack into your system. It also determines what user accounts are being targeted. It keeps track of the frequency of attempts from each host. Additionally, upon discovering a repeated attack host, the /etc/hosts.deny file is updated to prevent future break-in attempts from that host. An email report can be sent to a system admin and you may be alarmed to see how many hackers attempted to gain access to your server.
Secure SSH server attacks using DenyHosts tool for Linux servers.
Features
– Parses /var/log/secure to find all login attempts and filters failed and successful attempts.
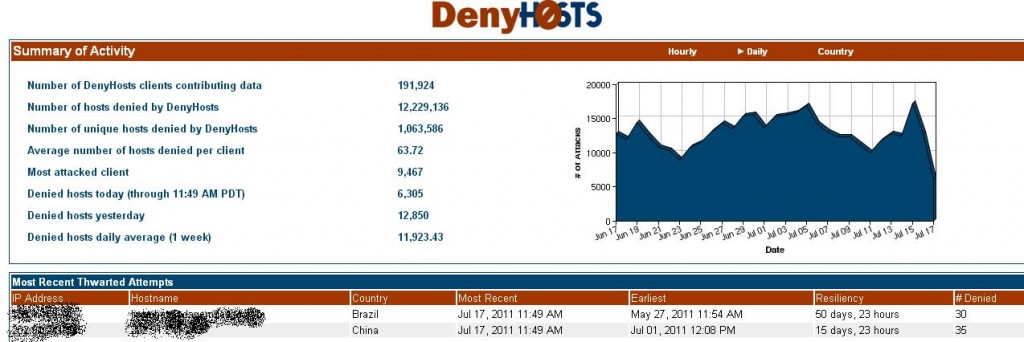
– Synchronization mode (new in 2.0) allows DenyHosts daemons the ability to share data via a centralized server to proactively thwart attacks.
– Can be run from the command line, cron or as a daemon (new in 0.9)
– Records all failed login attempts for the user and offending host
– For each host that exceeds a threshold count, records the evil host
– Keeps track of each non-existent user (eg. sdadasd) when a login attempt failed.
– Keeps track of each existing user (eg. root) when a login attempt failed.
– Keeps track of each offending host (with 0.8+ these hosts can be purged if the associated entry in /etc/hosts.deny is
expired)
– Keeps track of suspicious logins (that is, logins that were successful for a host that had many login failures)
– Keeps track of the file offset, so that you can reparse the same file (/var/log/secure) continuously (until it is rotated).
– When the log file is rotated, the script will detect it and parse from the beginning.
– Appends /etc/hosts.deny and adds the newly banned hosts
– Optionally sends an email of newly banned hosts and suspicious logins.
– Keeps a history of all user, host, user/host combo and suspicious logins encountered which includes the data and number of corresponding failed login attempts.
– Maintains failed valid and invalid user login attempts in separate files, such that it is easy to see which valid user is
under attack (which would give you the opportunity to remove the account, change the password or change it’s default shell to something like /sbin/nologin
– Upon each run, the script will load the previously saved data and re-use it to append new failures.
– Resolves IP addresses to hostnames, if available (new in v0.6.0).
– /etc/hosts.deny entries can be expired (purge) at a user specified time (new in 0.8)
Secure SSH server attacks in centos
Install DenyHosts on RHEL 6.3/6.2/6.1/6/5.8, CentOS 6.3/6.2/6.1/6/5.8 and Fedora 17,16,15,14,13,12 systems using epel repository.
By default DenyHosts tool is not included in the Linux systems, we need to install it using third party EPEL repository.
## RHEL/CentOS 7 64-Bit ##
# wget http://dl.fedoraproject.org/pub/epel/7/x86_64/e/epel-release-7-5.noarch.rpm # rpm -ivh epel-release-7-5.noarch.rpm
## RHEL/CentOS 6 32-Bit ##
# wget http://download.fedoraproject.org/pub/epel/6/i386/epel-release-6-8.noarch.rpm # rpm -ivh epel-release-6-8.noarch.rpm
## RHEL/CentOS 6 64-Bit ##
# wget http://download.fedoraproject.org/pub/epel/6/x86_64/epel-release-6-8.noarch.rpm # rpm -ivh epel-release-6-8.noarch.rpm
# yum install denyhosts
Once the Denyhosts installed, make sure to whitelist your own IP address, so you will never get locked out. To do this, open a file /etc/hosts.allow.
# vi /etc/hosts.allow
sshd: <yourIp> sshd: <yourIP>
Configuring Email Alerts
# vi /etc/denyhosts.conf
change ADMIN_EMAIL and SMTP_FROM details. ADMIN_EMAIL = [email protected] SMTP_FROM = DenyHosts <nobody@localhost> SMTP_SUBJECT = DenyHosts Report from $[HOSTNAME]
# chkconfig denyhosts on # service denyhosts start
To watch denyhosts ssh logs for how many attackers and hackers are attempted to gain access to your server.
# tail -f /var/log/secure
Add your IP Addresses Permanently in whitelist
# vi /var/lib/denyhosts/allowed-hosts
### We mustn't block localhost 127.0.0.1 110.18.15.11
You can view denied ipaddress in /etc/hosts.deny
[root@localhost ~]# cat /etc/hosts.deny
# # hosts.deny This file contains access rules which are used to deny connections to network services that either use # the tcp_wrappers library or that have been # started through a tcp_wrappers-enabled xinetd. ## The rules in this file can also be set up in /etc/hosts.allow with a 'deny' option instead. # # DenyHosts: Thu Mar 5 03:26:50 2015 | sshd: 192.168.1.110 sshd: 192.168.1.110 # DenyHosts: Thu Mar 5 03:26:50 015 | sshd: 192.168.1.11 sshd: 192.168.1.11
In order to remove or delete banned IP address completely. You need to edit the following files and remove the IP address.
# vi /etc/hosts.deny # vi /var/lib/denyhosts/hosts # vi /var/lib/denyhosts/hosts-restricted # vi /var/lib/denyhosts/hosts-root # vi /var/lib/denyhosts/hosts-valid # vi /var/lib/denyhosts/users-hosts
Once completed, restart denyhost service.
service denyhosts start
Thats all!!
DenyHosts v2.6 release contains a minor DoS security fix and some minor bug fixes. The DoS security issue affects all versions of DenyHosts prior to v2.6. All users are urged to upgrade to DenyHosts v2.6. Consult the Changelog for the gory details.